- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
Zoeken
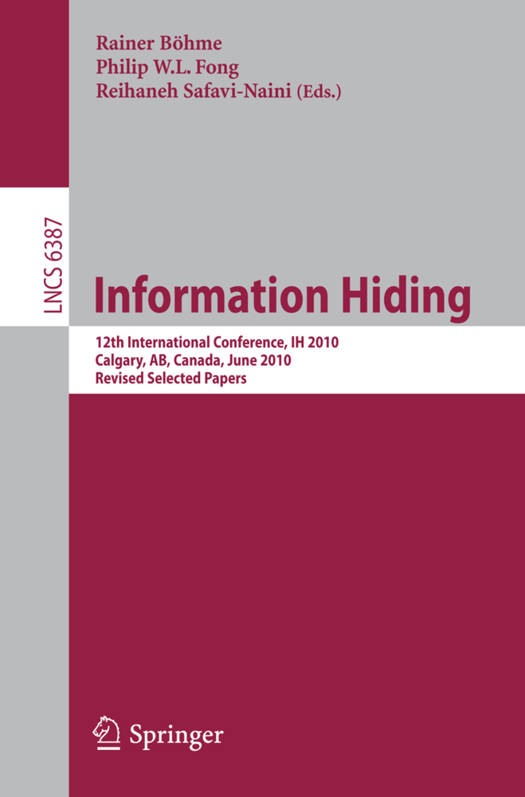
Information Hiding
12th International Conference, Ih 2010, Calgary, Ab, Canada, June 28-30, 2010, Revised Selected Papers
€ 53,45
+ 106 punten
Omschrijving
IH 2010 was the 12th Information Hiding Conference, held in Calgary, Canada, June 28-30, 2010. This series of conferences started with the First Workshop on Information Hiding, held in Cambridge, UK in May 1996. Since then, the conference locations have alternated between Europe and North America. The conference has been held annually since 2005. For many years, information hiding has captured the imagination of - searchers. This conference series aims to bring together a number of closely related research areas, including digital watermarking, steganography and s- ganalysis, anonymity and privacy, covert and subliminal channels, ?ngerpri- ing and embedding codes, multimedia forensics and counter-forensics, as well as theoretical aspects of information hiding and detection. Since its inception, the conference series has been a premier forum for publishing research in these areas. This volume contains the revised versions of 18 accepted papers (incor- rating the comments from members of the Program Committee), and extended abstracts of two (out of three) invited talks. The conference received 39 anonymous submissions for full papers. The task of selecting 18 of them for presentation was not easy. Each submission was reviewed by at least three members of the Program Committee or external - viewers reporting to a member of the Program Committee. In the case of - authorship by a Program Committee member, ?ve reviews were sought. There is no need to say that no member of the Program Committee reviewed his or her own work. Each paper was carefully discussed until consensus was reached.
Specificaties
Betrokkenen
- Uitgeverij:
Inhoud
- Aantal bladzijden:
- 277
- Taal:
- Engels
- Reeks:
- Reeksnummer:
- nr. 6387
Eigenschappen
- Productcode (EAN):
- 9783642164347
- Verschijningsdatum:
- 8/10/2010
- Uitvoering:
- Paperback
- Formaat:
- Trade paperback (VS)
- Afmetingen:
- 155 mm x 234 mm
- Gewicht:
- 417 g
Alleen bij Standaard Boekhandel
+ 106 punten op je klantenkaart van Standaard Boekhandel
Beoordelingen
We publiceren alleen reviews die voldoen aan de voorwaarden voor reviews. Bekijk onze voorwaarden voor reviews.