- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
Zoeken
Reeksen: boeken uit de reeks Security
-
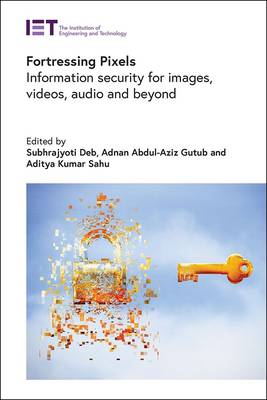
Fortressing Pixels
- Hardcover | Engels | Security
- Emerging and pivotal technologies such as artificial intelligence and deep learning, cloud computing, internet of things, blockchain, encryption, and ... Lees meer
€ 242,95€ 242,95 -
Voice Biometrics
- Hardcover | Engels | Security
- Voice biometrics are being implemented globally in large scale applications such as remote banking, government e-services, transportation and building... Lees meer
€ 242,95€ 242,95 -
Nature-Inspired Cyber Security and Resiliency
- Hardcover | Engels | Security
- With the rapid evolution of cyberspace, computing, communications and sensing technologies, organizations and individuals rely more and more on new ap... Lees meer
€ 275,45€ 275,45 -
Mobile Biometrics
- Hardcover | Engels | Security
- Mobile biometrics - the use of physical and/or behavioral characteristics of humans to allow their recognition by mobile/smart phones - aims to achiev... Lees meer
€ 307,95€ 307,95 -
Authentication Technologies for Cloud Computing, Iot and Big Data
- Hardcover | Engels | Security
- Critical systems and infrastructure rely heavily on ICT systems and networks where security issues are a major concern. Authentication methods verify ... Lees meer
€ 267,45€ 267,45 -
Age Factors in Biometric Processing
- Hardcover | Engels | Security
- As biometrics-based identification and identity authentication become increasingly widespread in their deployment, it becomes correspondingly importan... Lees meer
€ 150,95€ 150,95 -
Machine Learning, Blockchain Technologies and Big Data Analytics for Iots
- Hardcover | Engels | Security
- Internet of Things (IoTs) are now being integrated at a large scale in fast-developing applications such as healthcare, transportation, education, fin... Lees meer
€ 299,45€ 299,45 -
Privacy by Design for the Internet of Things
- Hardcover | Engels | Security
- Privacy by design is a proactive approach that promotes privacy and data protection compliance throughout project lifecycles when storing or accessing... Lees meer
€ 242,95€ 242,95 -
User-Centric Privacy and Security in Biometrics
- Hardcover | Engels | Security
- The interplay of privacy, security and user-determination is an important consideration in the roll-out of biometric technologies. It brings into play... Lees meer
€ 331,95€ 331,95 -
Iris and Periocular Biometric Recognition
- Hardcover | Engels | Security
- Iris recognition technologies for identity management are already deployed globally in several large-scale nationwide biometric projects and are curre... Lees meer
€ 331,95€ 331,95 -
Explainable Artificial Intelligence (Xai) for Next Generation Cybersecurity
- Hardcover | Engels | Security
- As AI technologies progress and influence more facets of our lives, the requirement for openness and interpretability becomes increasingly important. ... Lees meer
€ 250,95€ 250,95 -
Hand-Based Biometrics
- Hardcover | Engels | Security
- Hand-based biometrics identifies users by unique features in their hands, such as fingerprints, palmprints, hand geometry, and finger and palm vein pa... Lees meer
€ 267,45€ 267,45 -
Physical Layer Security for Wireless Sensing and Communication
- Hardcover | Engels | Security
- Wireless physical layer (PHY) secrecy has attracted much attention due to the broadcast nature of the wireless medium. To this end, researchers have b... Lees meer
€ 250,95€ 250,95 -
Cybersecurity in Banking
Shriram K Vasudevan, Sini Raj Pulari, T S Murugesh, Subashri Vasudevan
- Hardcover | Engels | Security
- Technology plays a pivotal role in today's financial landscape. Ensuring cyber security and safety in the banking sector has become paramount. The per... Lees meer
€ 242,95€ 242,95 -
Engineering Secure Internet of Things Systems
- Hardcover | Engels | Security
- The Internet of Things (IoT) - the emerging global interconnection of billions of 'smart' devices - will be collecting increasing amounts of private a... Lees meer
€ 291,45€ 291,45 -
Information Security
- Hardcover | Engels | Security
- The rapid advancements in telecommunications, computing hardware and software, and data encryption, and the widespread use of electronic data processi... Lees meer
€ 267,45€ 267,45 -
Data Security in Cloud Computing
- Hardcover | Engels | Security
- Cloud Computing has already been embraced by many organizations and individuals due to its benefits of economy, reliability, scalability and guarantee... Lees meer
€ 283,45€ 283,45
17 van 17 resultaten getoond