- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
Zoeken
Resultaten voor "Brij B Gupta"
-
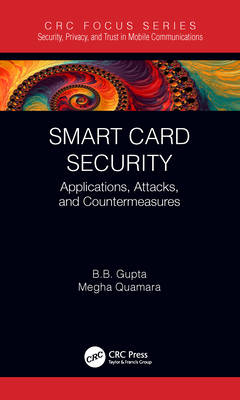
Smart Card Security
Brij B Gupta, Megha Quamara
- Hardcover | Engels | Security, Privacy, and Trust in Mobile Communications
- This book provides an overview of smart card technology and explores different security attacks and countermeasures associated with it. It covers the ... Lees meer
€ 117,95Levering 2 à 3 weken€ 117,95Levering 2 à 3 weken -
AI and Quantum Security
Brij B Gupta, Amiya Nayak
- Hardcover | Engels | Wireless Networks
- This book provides a comprehensive guide to integrating Artificial Intelligence (AI), Large Language Models (LLMs), and quantum-safe security mechanis... Lees meer
€ 70,45Levertermijn 1 à 4 weken€ 70,45Levertermijn 1 à 4 weken -
Online Social Networks Security
Brij B Gupta, Somya Ranjan Sahoo
- Paperback | Engels
- This book elaborates on various attacks on Social Networks with classifications, countermeasures and consequences. It also highlights some key contrib... Lees meer
€ 44,45Levering 2 à 3 weken€ 44,45Levering 2 à 3 weken -
Distributed Denial of Service (DDoS) Attacks
Brij B Gupta, Amrita Dahiya
- Paperback | Engels
- This book is designed for readers who have an interest in the cyber security domain, including students and researchers who are exploring different di... Lees meer
€ 44,45Levering 2 à 3 weken€ 44,45Levering 2 à 3 weken -
Secure Searchable Encryption and Data Management
Brij B Gupta, Mamta
- Hardcover | Engels
- This book provides every necessary detail required to develop the secure searchable encryption scheme using both symmetric and asymmetric cryptographi... Lees meer
€ 105,45Levering 2 à 3 weken€ 105,45Levering 2 à 3 weken -
A Beginner's Guide to Internet of Things Security
Brij B Gupta, Aakanksha Tewari
- Paperback | Engels
- This book focuses on security issues in the IoT environment. It analyzes the security problems of each layer separately and try to identity solutions.... Lees meer
€ 48,95Levering 2 à 3 weken€ 48,95Levering 2 à 3 weken -
Distributed Denial of Service (DDoS) Attacks
Brij B Gupta, Amrita Dahiya
- Hardcover | Engels
- This book is designed for readers who have an interest in the cyber security domain, including students and researchers who are exploring different di... Lees meer
€ 105,45Levering 2 à 3 weken€ 105,45Levering 2 à 3 weken -
Online Social Networks Security
Brij B Gupta, Somya Ranjan Sahoo
- Hardcover | Engels
- This book elaborates on various attacks on Social Networks with classifications, countermeasures and consequences. It also highlights some key contrib... Lees meer
€ 105,45Levering 2 à 3 weken€ 105,45Levering 2 à 3 weken -
Smart Card Security
Brij B Gupta, Megha Quamara
- Paperback | Engels | Security, Privacy, and Trust in Mobile Communications
- This book provides an overview of smart card technology and explores different security attacks and countermeasures associated with it. It covers the ... Lees meer
€ 39,95Levering 2 à 3 weken€ 39,95Levering 2 à 3 weken -
Secure Searchable Encryption and Data Management
Brij B Gupta, Mamta
- Paperback | Engels
- This book provides every necessary detail required to develop the secure searchable encryption scheme using both symmetric and asymmetric cryptographi... Lees meer
€ 44,45Levering 2 à 3 weken€ 44,45Levering 2 à 3 weken -
Cross-Site Scripting Attacks
Brij B Gupta, Pooja Chaudhary
- Paperback | Engels | Security, Privacy, and Trust in Mobile Communications
- Cross-Site Scripting Attacks: Classification, Attack, and Countermeasures is a comprehensive source which provides an overview of web-based vulnerabil... Lees meer
€ 44,45Levering 2 à 3 weken€ 44,45Levering 2 à 3 weken
11 van 11 resultaten getoond