- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
- Afhalen na 1 uur in een winkel met voorraad
- Gratis thuislevering in België vanaf € 30
- Ruim aanbod met 7 miljoen producten
Zoeken
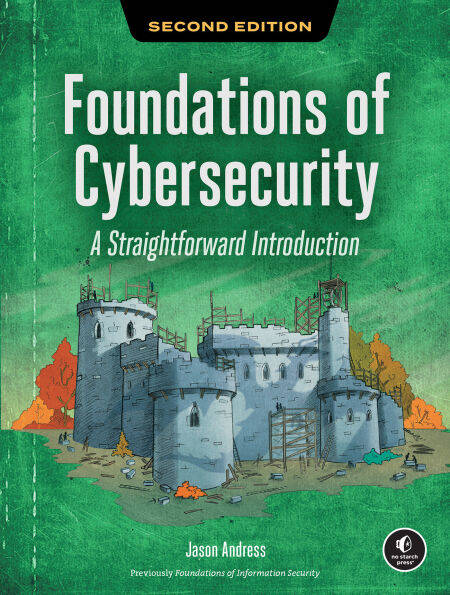
Foundations of Cybersecurity, 2nd Edition E-BOOK
A Straightforward Introduction
Jason Andress
E-book | Engels
€ 47,31
+ 47 punten
Uitvoering
Omschrijving
This comprehensive introduction to the information security field covers the industry’s essential concepts, using real-world security breaches to illustrate key lessons.
"An excellent starting point for future security professionals.”
—Help Net Security
Cybersecurity is a huge field, and breaking in can feel overwhelming. Where do you start when the territory spans everything from cryptography to cloud security to social engineering?
In Foundations of Cybersecurity, you’ll learn how security professionals actually think about protecting systems. You’ll start with core principles like authentication, authorization, and access control, then build outward into network defense, operating system hardening, application security, and security operations.
Each chapter introduces concepts in context, showing how they connect to real decisions you’ll face on the job.
This updated second edition covers:
How attackers think: the threat landscape, social engineering tactics, and the kill chain How defenders respond: SOC operations, incident response, and vulnerability assessment The business side: governance, risk management, compliance frameworks, and penetration testing Securing what’s new: AI systems, IoT devices, and cloud-native architectures Building your career: paths into security, certifications that matter, and the soft skills that separate good analysts from great ones
Hands-on projects throughout will have you apply what you’ve learned, from classifying real threat actors to designing detection rules to building a security awareness program.
Whether you’re coming from IT or a completely different field, this book gives you the conceptual foundation to understand what cybersecurity professionals do, why they do it, and how to become one.
"An excellent starting point for future security professionals.”
—Help Net Security
Cybersecurity is a huge field, and breaking in can feel overwhelming. Where do you start when the territory spans everything from cryptography to cloud security to social engineering?
In Foundations of Cybersecurity, you’ll learn how security professionals actually think about protecting systems. You’ll start with core principles like authentication, authorization, and access control, then build outward into network defense, operating system hardening, application security, and security operations.
Each chapter introduces concepts in context, showing how they connect to real decisions you’ll face on the job.
This updated second edition covers:
How attackers think: the threat landscape, social engineering tactics, and the kill chain How defenders respond: SOC operations, incident response, and vulnerability assessment The business side: governance, risk management, compliance frameworks, and penetration testing Securing what’s new: AI systems, IoT devices, and cloud-native architectures Building your career: paths into security, certifications that matter, and the soft skills that separate good analysts from great ones
Hands-on projects throughout will have you apply what you’ve learned, from classifying real threat actors to designing detection rules to building a security awareness program.
Whether you’re coming from IT or a completely different field, this book gives you the conceptual foundation to understand what cybersecurity professionals do, why they do it, and how to become one.
Specificaties
Betrokkenen
- Auteur(s):
- Uitgeverij:
Inhoud
- Aantal bladzijden:
- 328
- Taal:
- Engels
Eigenschappen
- Productcode (EAN):
- 9781718504417
- Verschijningsdatum:
- 18/05/2026
- Uitvoering:
- E-book
- Formaat:
- ePub
Alleen bij Standaard Boekhandel
+ 47 punten op je klantenkaart van Standaard Boekhandel
Beoordelingen
We publiceren alleen reviews die voldoen aan de voorwaarden voor reviews. Bekijk onze voorwaarden voor reviews.