- Afhalen na 1 uur in een winkel met voorraad
- In januari gratis thuislevering in België
- Ruim aanbod met 7 miljoen producten
- Afhalen na 1 uur in een winkel met voorraad
- In januari gratis thuislevering in België
- Ruim aanbod met 7 miljoen producten
Zoeken
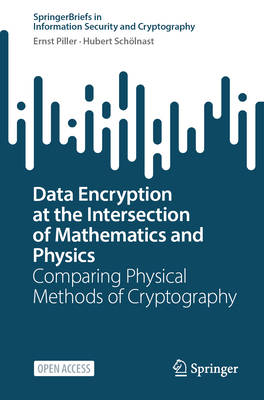
Data Encryption at the Intersection of Mathematics and Physics
Comparing Physical Methods of Cryptography
Ernst Piller, Hubert Schölnast
€ 32,45
+ 64 punten
Omschrijving
Data is becoming increasingly important, and so is data security. This book is aimed at anyone interested in high data security in telecommunications and data storage, especially IT security experts, procurers, decision-makers, consultants, and computer scientists. Anyone involved in procurement in this field makes decisions about algorithms, technologies, and providers, and thus also about infrastructure and security. The generation and distribution of keys for data encryption play a central role in this. Because security assessments for mathematical methods are based on assumptions, physical methods are becoming interesting in the high-security sector. They promise to link security more closely to the laws of nature. This raises the key question: Which technology is suitable for which application scenario, and what assumptions, costs, and operational risks are involved? This book provides answers and, for the first time, compares QKD (Quantum Key Distribution), RKD (Radio-signal Key Distribution), and MKD (Memory Key Distribution) within a common, transparent criteria framework: technology-neutral, practical, and easy to understand. The evaluation covers secret key rates, range/attenuation, robustness, costs, infrastructure, portability, standardization, IT security, and security risks (implementation, integration, post-processing, side channels). The evaluations are deliberately presented not as a ranking, but as a decision-making aid. The book will be published in print and as open access. QKD derives its security from the laws of quantum physics, but secret key rates decrease with increasing attenuation. Key management systems connect short QKD distances over longer distances, but only at the cost of additional attack surfaces ("trusted nodes"). Its use for mobile applications fails due to a lack of technical maturity. Very high financial costs and high maintenance requirements for QKD solutions make them unattractive in high-security environments. RKD utilizes the reciprocal physical properties of a radio link and scores points for its low technical complexity, excellent suitability for mobile applications (e.g., vehicles or drones), and very low costs. However, RKD falls far short of the key rates achieved by QKD solutions and is still limited to shorter distances. In addition, there is no established infrastructure for distributing key material to more than two partners. MKD takes a completely different approach: each party produces key material, stores it on a data carrier, and transports it physically to the other party. Because MKD can securely transfer 16 TB of key material in a single transport, only MKD has the potential to continuously provide a one-time pad (OTP) and thus provably 100% secure data encryption. The price is organizational responsibility: secure generation, storage, transport, and documented chain of custody. The book examines data security for telecommunications and data storage, discusses encryption modes for OTP, and addresses the question of when "OTP proximity" makes more sense than theoretical purity. The result of approximately one year of source-critical research and the comparison of literature, manufacturer specifications, and practical observations with systematic cross-checking and our own R&D activities, this book helps to justify architecture and procurement decisions, locate risks (side channels, misconfigurations, logistical vulnerabilities), and separate "security gains" from "new attack surfaces."
Specificaties
Betrokkenen
- Auteur(s):
- Uitgeverij:
Inhoud
- Aantal bladzijden:
- 157
- Taal:
- Engels
- Reeks:
Eigenschappen
- Productcode (EAN):
- 9783032247636
- Verschijningsdatum:
- 20/06/2026
- Uitvoering:
- Paperback
- Formaat:
- Trade paperback (VS)
- Afmetingen:
- 155 mm x 235 mm
Alleen bij Standaard Boekhandel
+ 64 punten op je klantenkaart van Standaard Boekhandel
Beoordelingen
We publiceren alleen reviews die voldoen aan de voorwaarden voor reviews. Bekijk onze voorwaarden voor reviews.